Network Security Zones
One of the most foundational ways to accomplish this is through the use of network security zones, which we'll take a look at in this blog post. We'll cover common security zone types, and also zone filtering policy considerations for each.
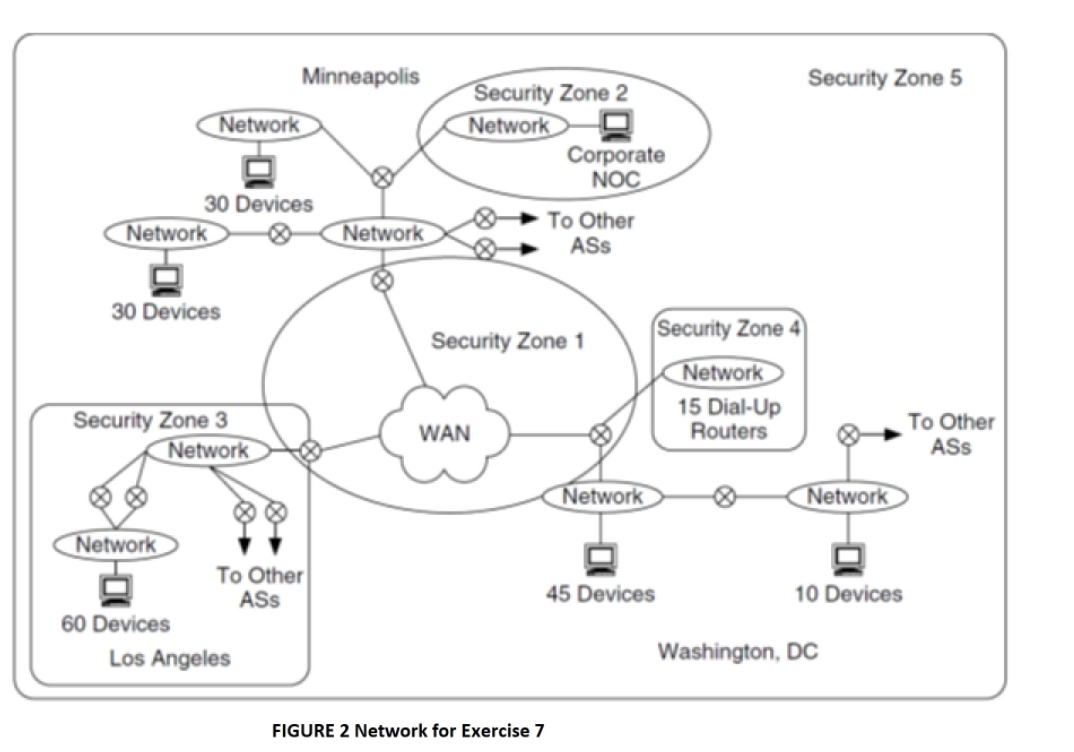
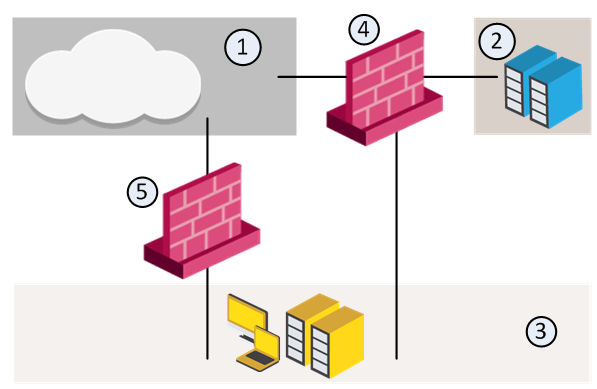
Solved Figure 2 shows five security zones required by the
Overview of Security Zones
Security Zones
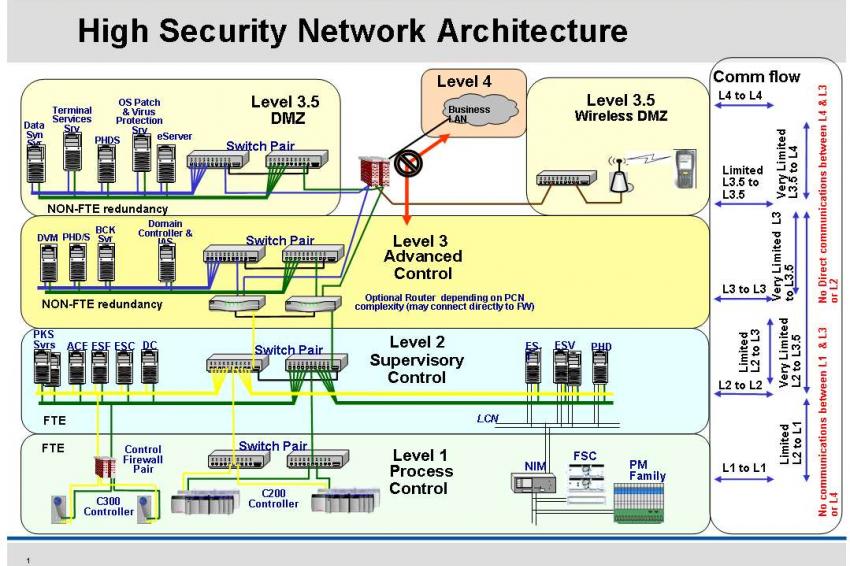
Cyber Security for Industrial Control Systems
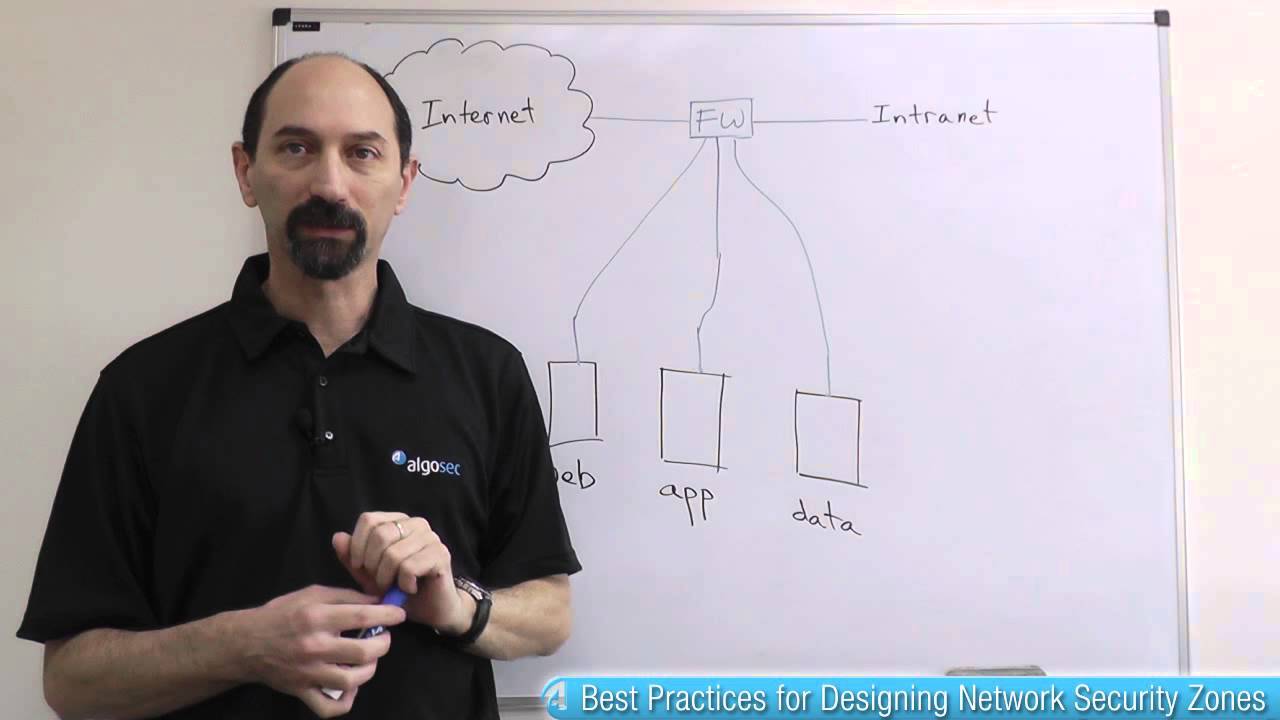
Lesson 3: Common Mistakes and Best Practices for Designing Network Security Zones - AlgoSec
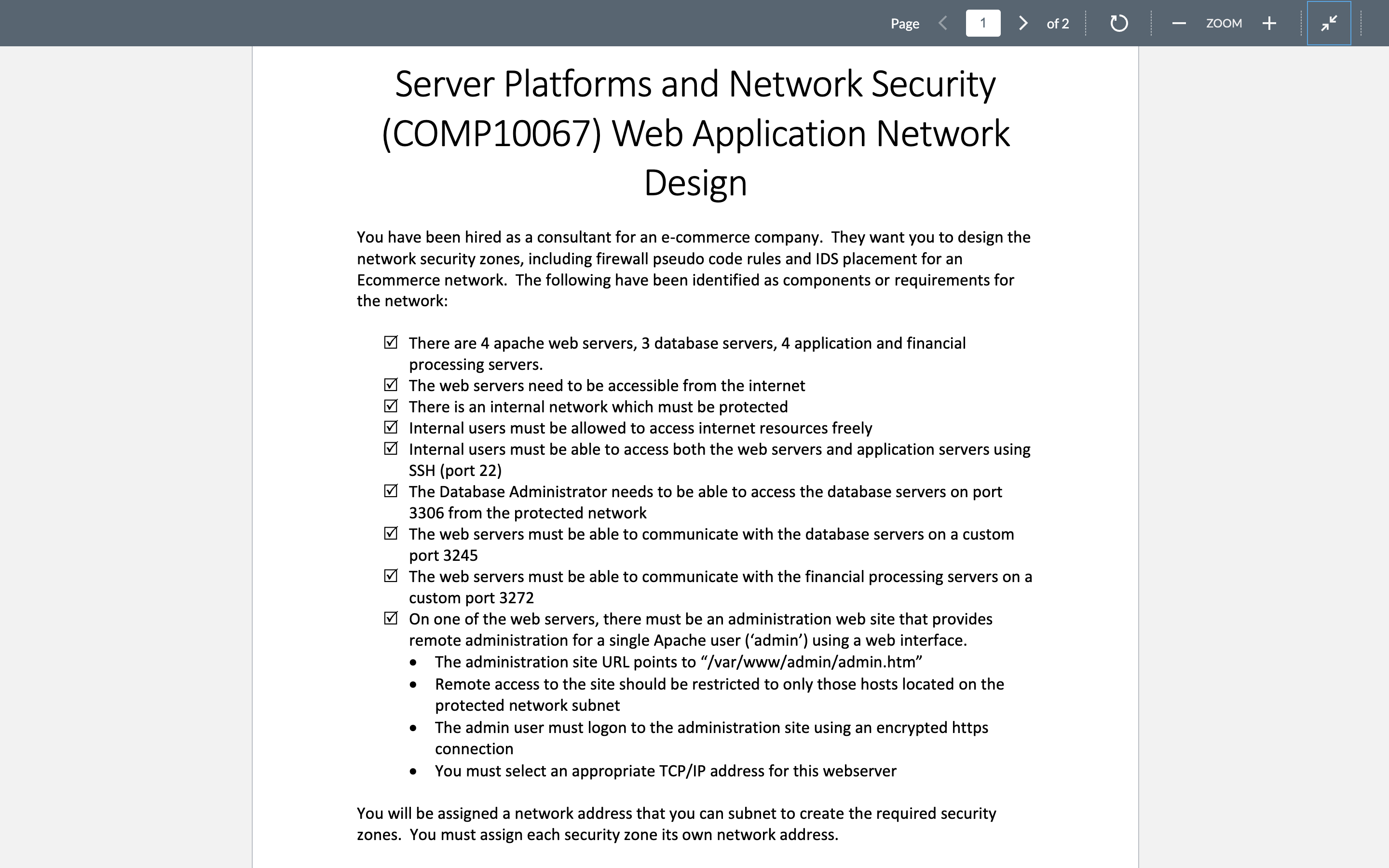
Solved Design You have been hired as a consultant for an

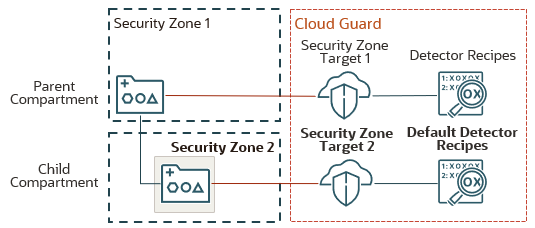
Enforce security policies with Custom Security Zones
Baseline security requirements for network security zones (version 2.0) - ITSP.80.022 - Canadian Centre for Cyber Security
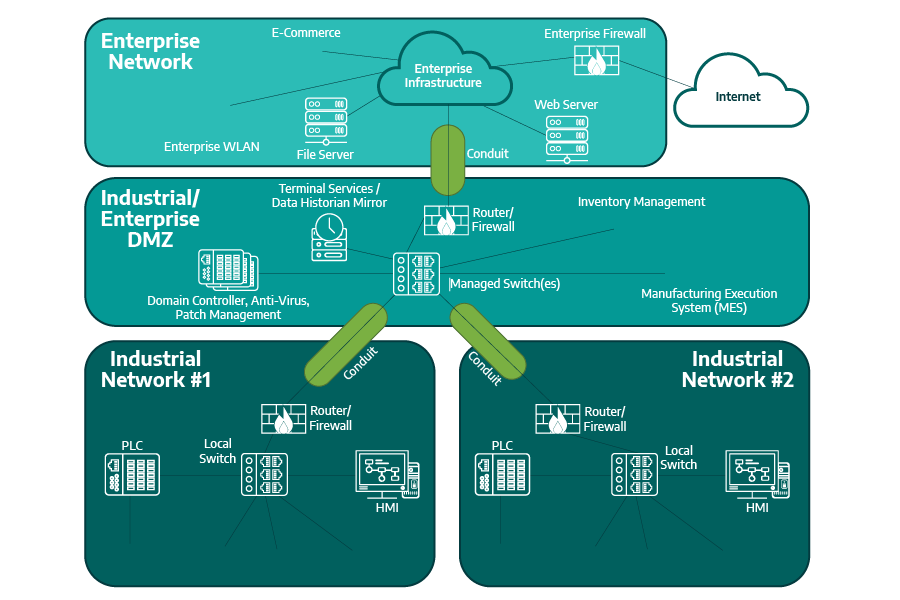
Key Concepts of ISA/IEC 62443: Zones & Security Levels

What Are the Benefits of Network Segmentation?
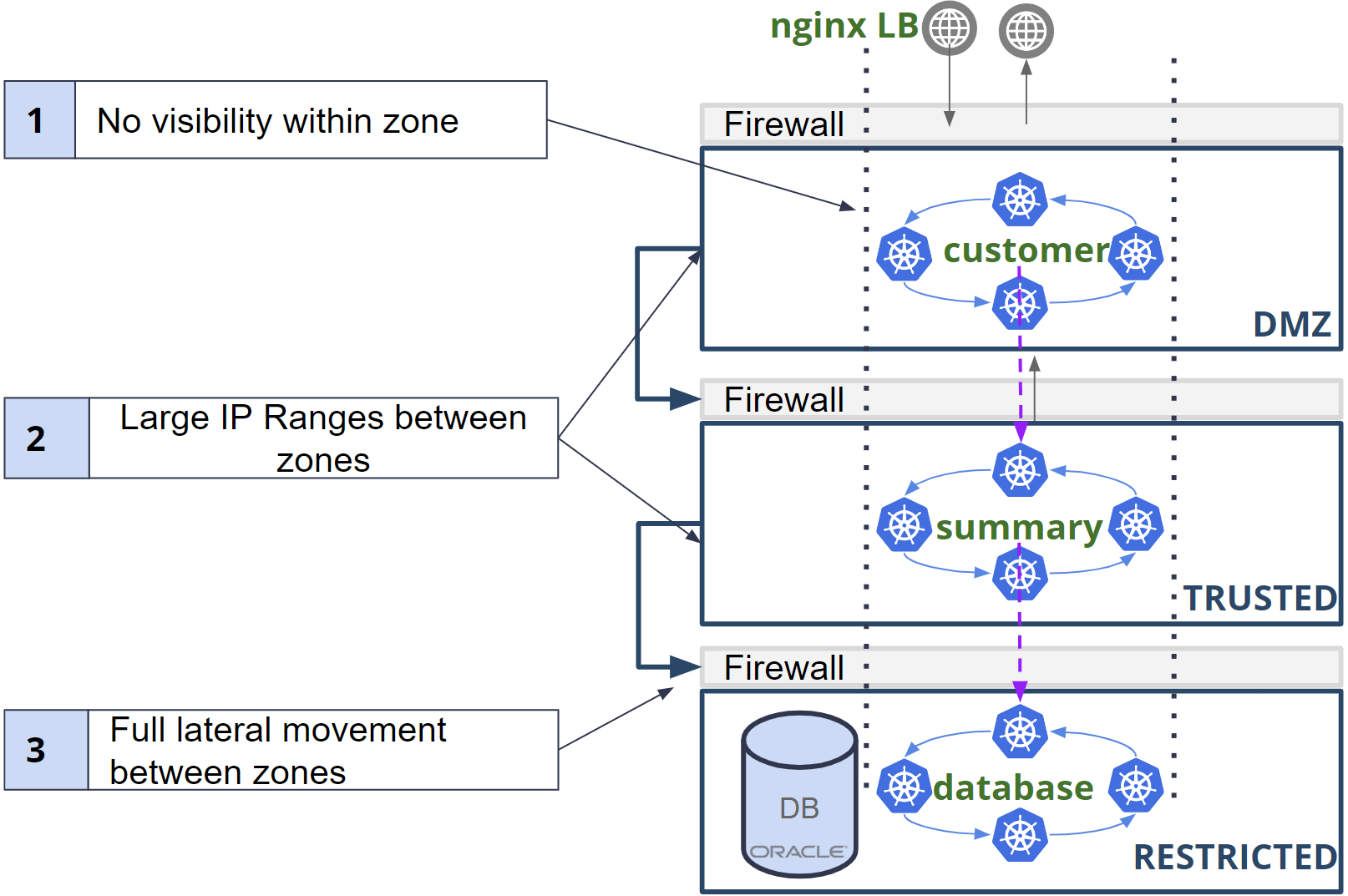
Kubernetes network security foundations: Get started on building your Kubernetes network security policies with Calico!
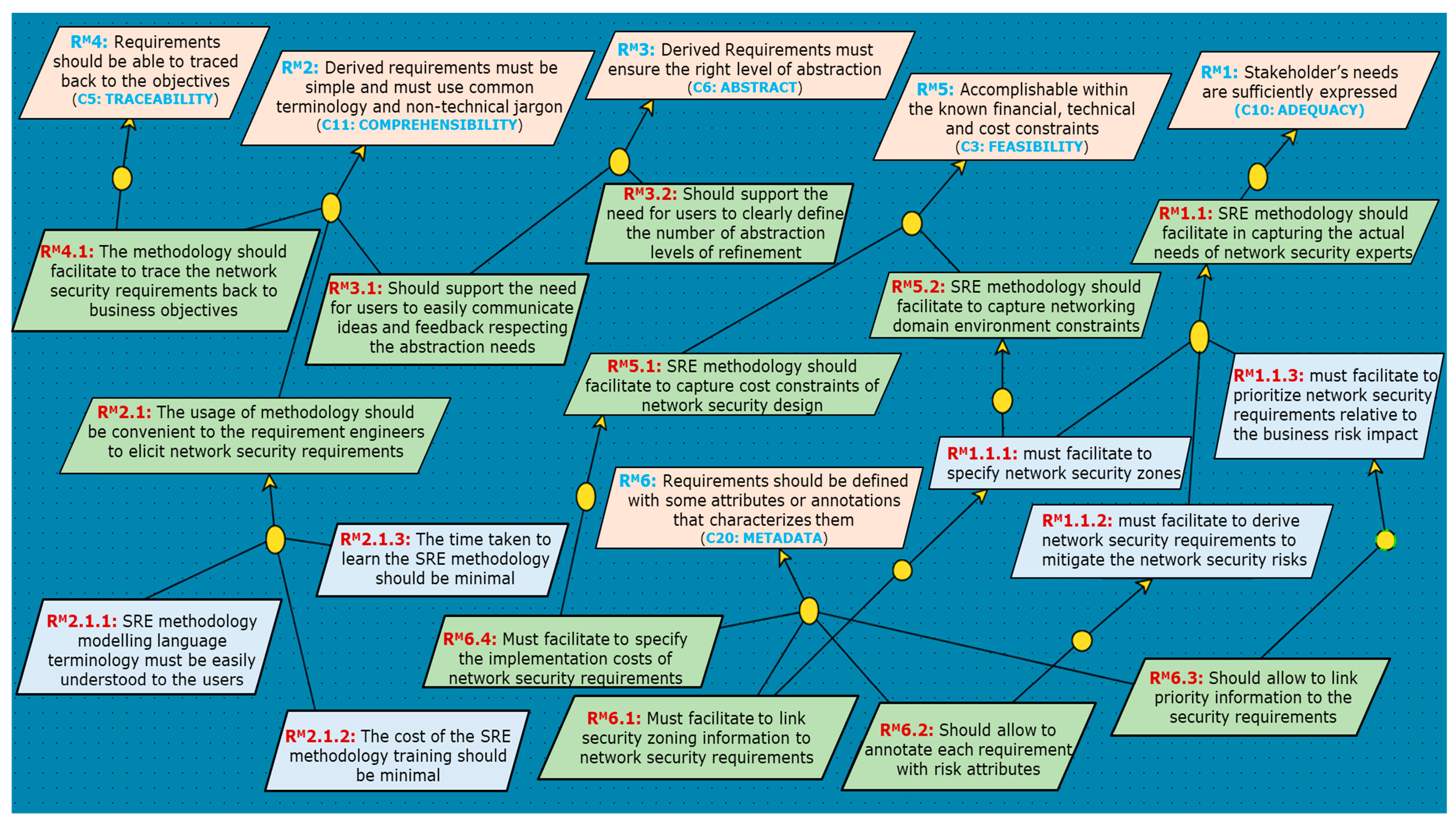
JCP, Free Full-Text